Arch Linux and Windows 10 (UEFI + Encrypted) Install Guide
This post details the installation process for my work and personal computers. At a high-level, my setup is a dualboot system running Windows 10 and Arch Linux. The Windows partition is encrypted with VeraCrypt and the Linux partition with LUKS. The post will detail the step-by-step. The video link below providers more context on how all the pieces fit together.
Click here to watch the video version of this content.Installation Media
This section covers creating installation media for Windows and Arch Linux. You'll need 2 USB drives sized to >= 8GB. These steps cover media creation from Windows (for the Windows 10 ISO) and Linux (for the Arch Linux ISO) workstations. There are many alternative ways to create installation media. If you choose to go with an alternative, skip this section.
Windows Installation Media
As of Windows 10, Microsoft requires you to download a tool to create windows installation media.
This .exe requires a Windows host to create the installation media. If you do not have a Windows
host to run this installer, Microsoft offers a USB for purchase.
Windows did not historically have this restriction. For example, Windows 8. You could follow this guide using Window 8. To create installation media directly from an ISO, consider WoeUSB.
Arch Linux Installation Media
-
Download the Arch Linux ISO.
-
Insert a USB drive.
-
List block devices and determine the device name.
lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT sda 8:0 1 29.2G 0 disk |-sda1 8:1 1 602M 0 part `-sda2 8:2 1 64M 0 part nvme0n1 259:0 0 477G 0 disk |-nvme0n1p1 259:1 0 512M 0 part /boot `-nvme0n1p2 259:2 0 476.4G 0 part `-cryptroot\x5cx2callow-discards\x5cx2cheader 254:0 0 476.4G 0 crypt `-vg0-root 254:1 0 476.4G 0 lvm /In the above example, the USB drive is
sda. -
Write the ISO to the device using dd.
dd bs=4M if=path/to/archlinux.iso of=/dev/sdx status=progress oflag=syncdd: copies and converts a file based on arguments.bs: amount of bytes to write at a time.if: specify a file to read rather than stdin.of: specify a file to write to rather than stdout.status: level to log to stderr; progress shows periodic transfer stats.oflag: set to sync synchronizes I/O for data and metadata.
BIOS Settings
-
Boot into BIOS.
Often accomplished by hitting F2 on start-up.
-
Verify UEFI booting is enabled.
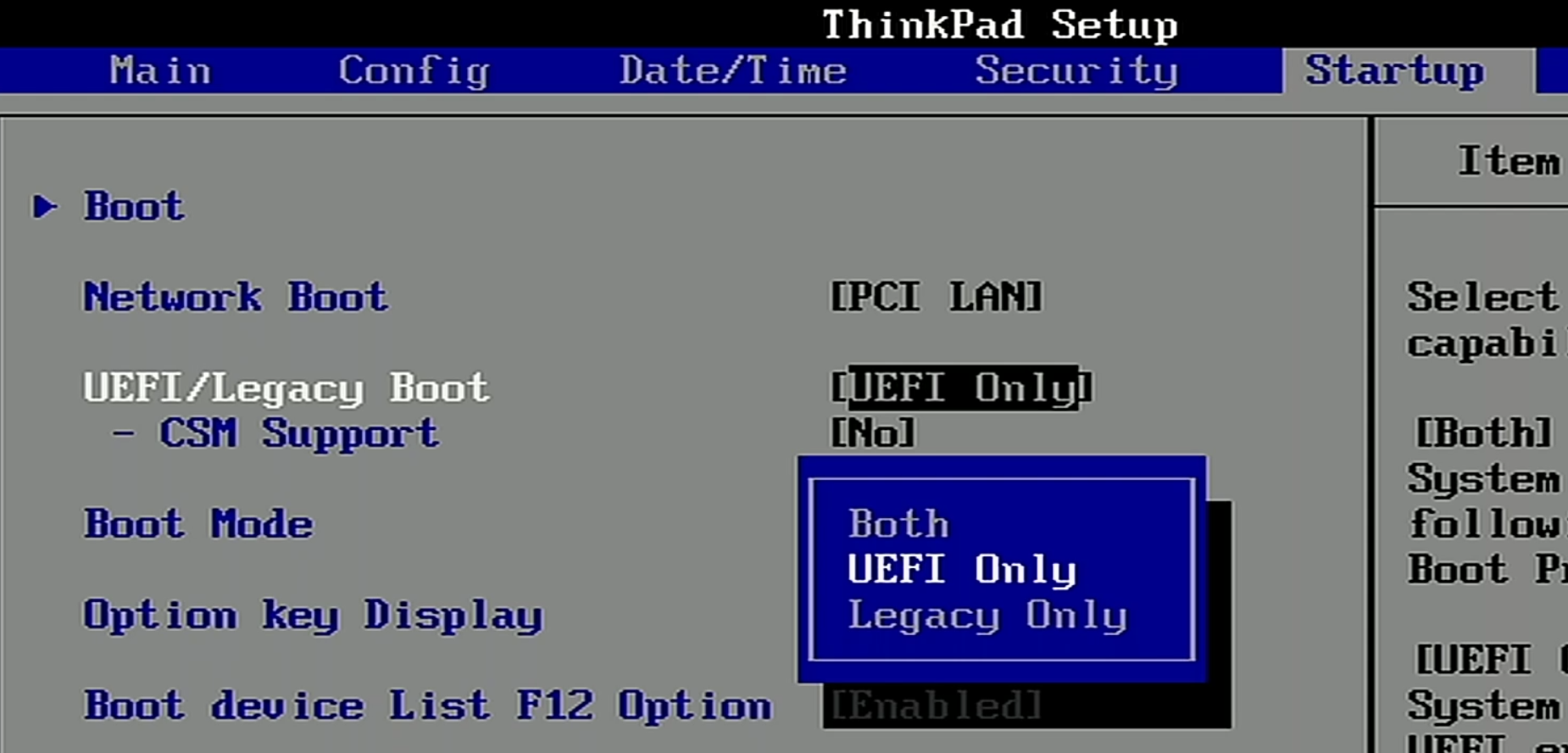
-
Verify Secure Boot is disabled.
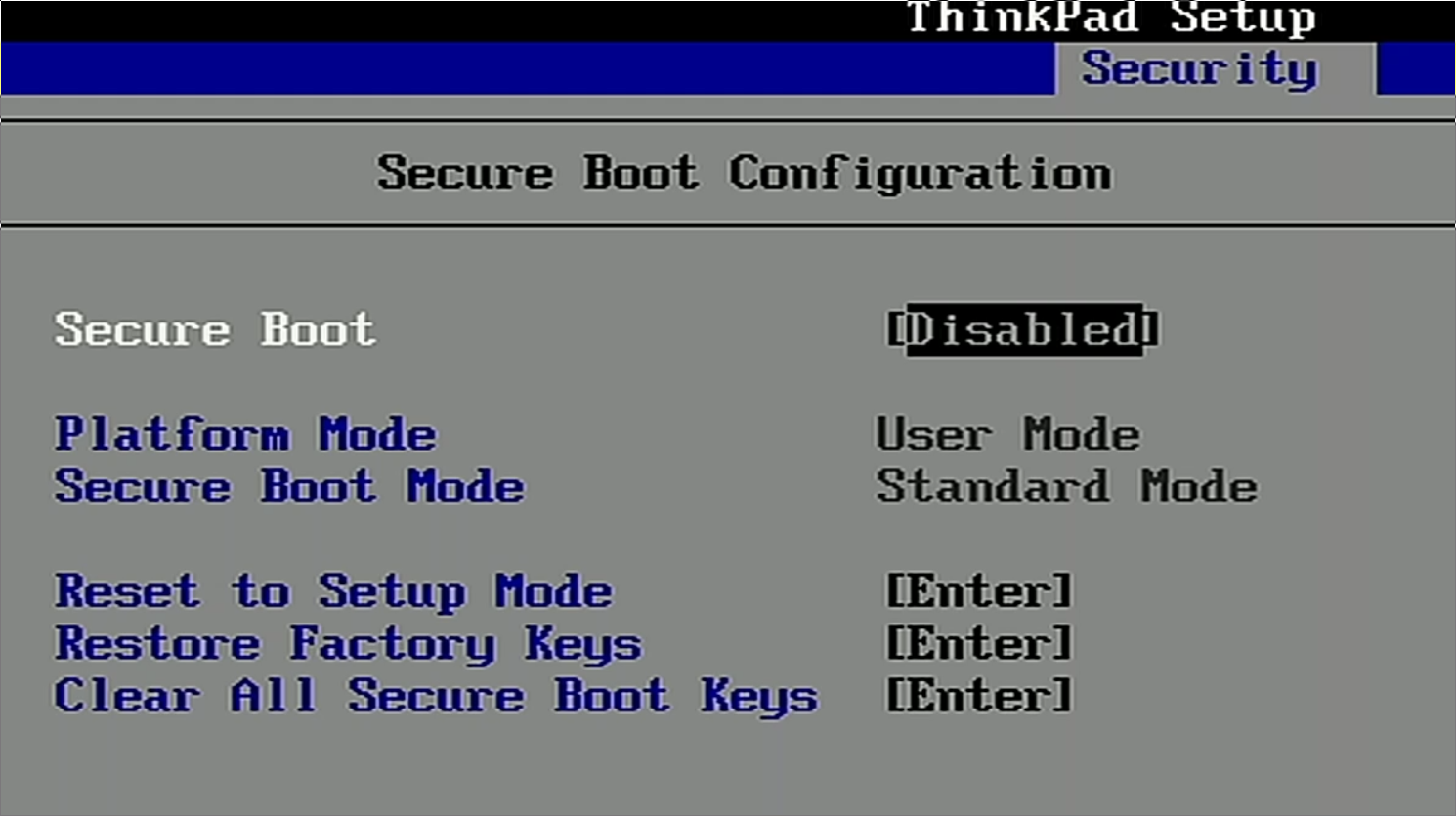
Arch Linux can be installed with Secure Boot. See https://wiki.archlinux.org/index.php/Secure_Boot
Installing Windows
This section covers installing Windows. Installing it first allows reuse of the Windows-created EFI partition. Using VeraCrypt, the Windows partition will be encrypted.
-
Insert the USB containing Windows.
-
Power on.
-
While booting, open the device boot menu.
Often achieved by hitting F12 during boot.
-
Select the USB device in UEFI mode.
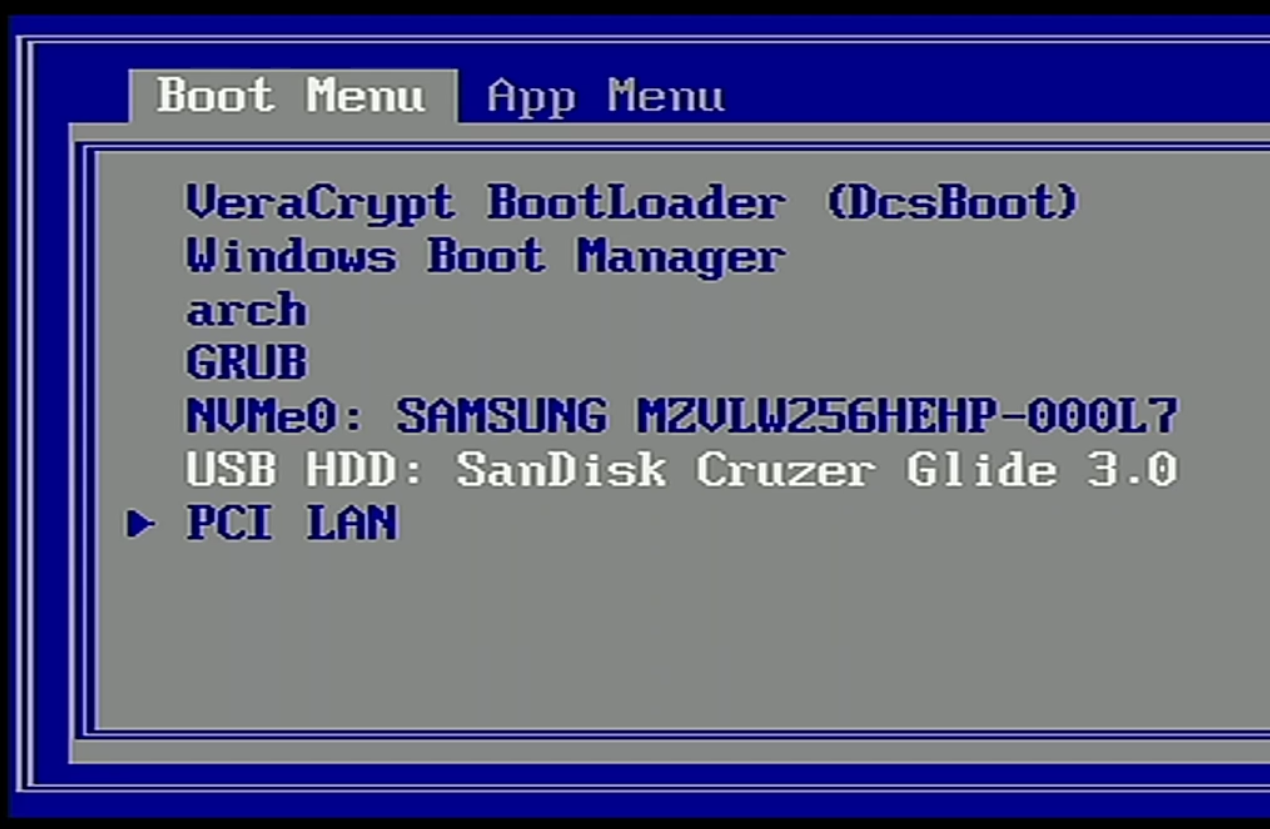
If you boot in legacy mode, the Arch UEFI installation will not work.
-
Select the language to install and click Next.
-
Click Install now.
-
Enter your product key and click Next.
-
Accept the license terms and click Next.
-
Click Custom: Install Windows only (advanced).
-
Delete all existing partitions.

-
Create a new partition of the size you'd like Windows to occupy.

Windows creates additoinal partitions including the 100.0MB System partition that will act as the EFI partition. 1. Click Next and wait for Windows to install.

After the installation completes, the machine will reboot.
-
After reboot, go through the Windows setup procedure.

-
Open Control Panel.
-
In the top right search, enter
power.
-
Click
Change what the power buttons do. -
Click
Change settings that are unavailble. -
Uncheck
Turn on fast startup (recommended).
To understand why fast startup is not recommended, see https://wiki.archlinux.org/index.php/Dual_boot_with_Windows#Fast_Start-Up
-
Open Start > Settings > Update & Security and Check for updates.
-
Allow all Windows updates to download and install before proceeding.
-
Download and install VeraCrypt.
-
Launch VeraCrypt.
-
From the menu bar, open System > Encrypt System Partition/Drive

-
Choose Normal.

-
Choose Encrypt the Windows system partition.

-
Choose Single-boot.
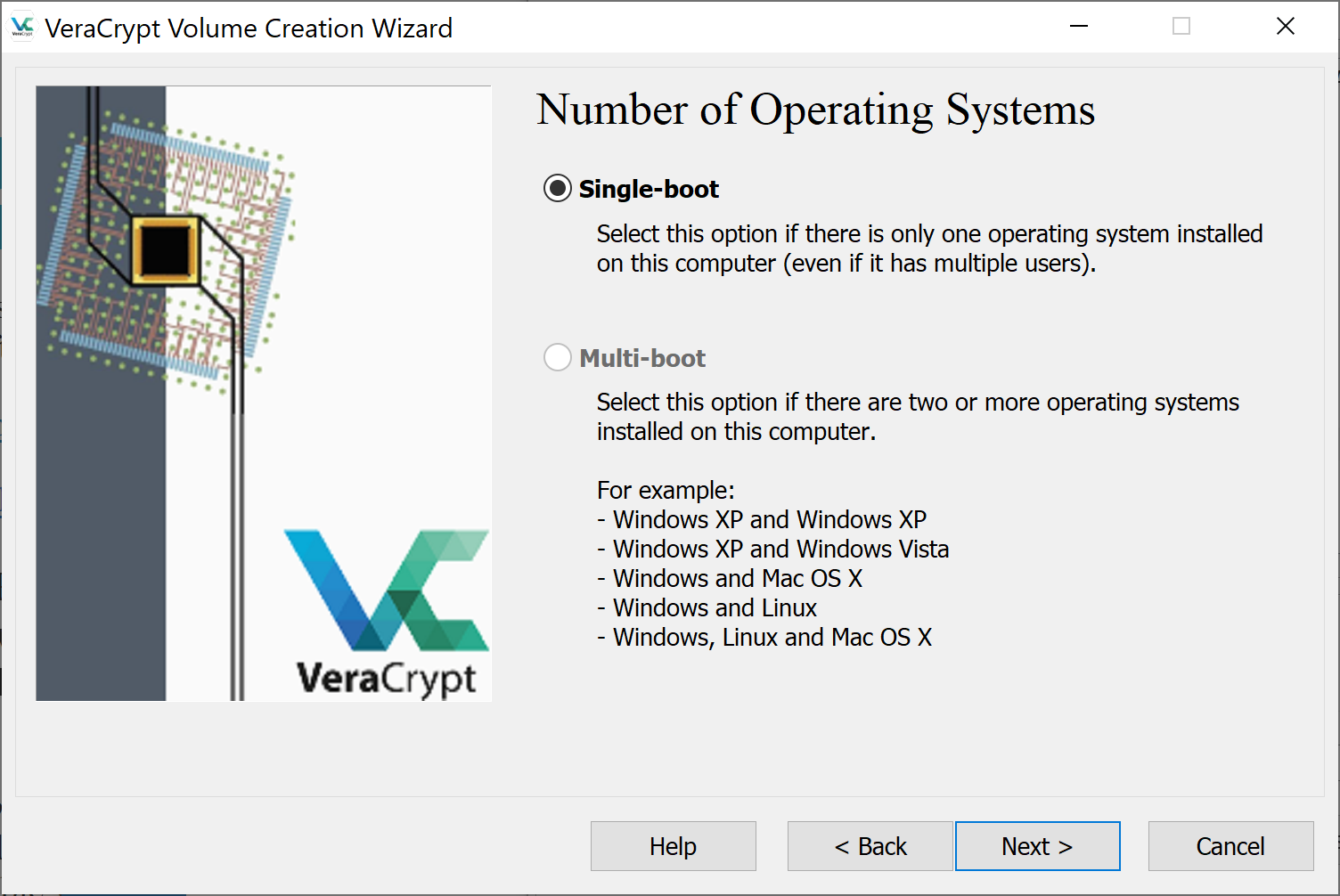
While you will have a multi-boot system eventually. This installation will have grub point to veracrypt that will then decrypt and point to windows. Thus, vercrypt needs to know nothing about Linux.
-
Choose your preferred encryption algorithm and click Next.
-
Create a strong password.
-
Allow VeraCrypt to collect random data.
-
If desired, create a rescue disk.
This will require a USB drive to save to.
-
Choose your preferred Wipe Mode.
-
Run the System Encryption Pretest.
This will require your machine to be restarted.
-
Upon restart, enter your encryption password when prompted.
-
Log back in to your Windows system.
-
VeraCrypt will pop back up to tell you the Pretest Completed.

-
Click Encrypt and run the encryption.
This will encrypt the file system and take several minutes.
-
Allow the encryption to complete.

-
Power off the machine.
Installing Arch Linux
This section covers installing Arch Linux. Using Linux Unified Key Setup (LUKS), the root partition will be encrypted.
-
Insert the USB containing Arch Linux.
-
Boot the machine.
-
While booting, open the device boot menu.
Often a key like F12 launches the boot menu.
-
Select the USB device.
If legacy boot is enabled on your system, assure you're choosing to boot the USB via UEFI.
-
At the Arch Boot Menu, hit
eat the menu to edit parameters. -
Add
nomodeset video=1280x760to the list of commands.
This boots the installer in lower resolution making the console easier to see.
-
Run
wifi-connectand select a wireless network.If plugged into ethernet, this step can be skipped.
-
Validate connectivity.
ping google.com PING google.com (216.58.193.206) 56(84) bytes of data. 64 bytes from lax02s23-in-f14.1e100.net time=809 ms 64 bytes from lax02s23-in-f14.1e100.net time=753 ms
After the steps above, I always start sshd (included in the archiso) and finish the installation process from another computer. This enables me to have access to copy and paste, editors, and browsers rather than the restricted terminal on my target machine. This is optional, but the steps below may make your experience better.
-
Set a root passwd for archiso.
passwd -
Enable
sshd.systemctl start sshd
-
Determine your local address using
ip a. -
From another machine, ssh in.
ssh root@${TARGET_MACHINE_IP}
From this point forward, I'm completing the installation from another Linux desktop. You can also use Windows (putty) or Mac.
Disk Partitioning
-
List block devices to determine the name of the drive.
lsblk NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT nvme0n1 259:0 0 477G 0 disk |-nvme0n1p1 259:1 0 512M 0 part /boot `-nvme0n1p2 259:2 0 476.4G 0 part `-cryptroot\x5cx2callow-discards\x5cx2cheader 254:0 0 476.4G 0 crypt `-vg0-root 254:1 0 476.4G 0 lvm /In the above, the drive is mapped to
/dev/nvme0n1. -
Launch cgdisk for the drive above.
cgdisk /dev/nvme0n1cgdiskis an ncurses-based GUID partition table manipulator. Unlike the command-onlyfdiskapproach,cgdiskprovides a text-menu for writing partitions. -
Select the free space.
-
Choose
[ New ].
-
Enter no value for First sector (chooses default).
This means the Linux partition starts directly at the end of the Windows partition. Some believe it is best to leave a small amount of free space between partitions. However, I have not had issues with this.
-
Enter 512Mib for size in sectors.
This is the end size of the partition.
-
Enter no value for Hex code or GUID (chooses default).
Default is 8300, Linux filesystem. A list can be found at https://gist.github.com/gotbletu/a05afe8a76d0d0e8ec6659e9194110d2
-
Name the partition
boot.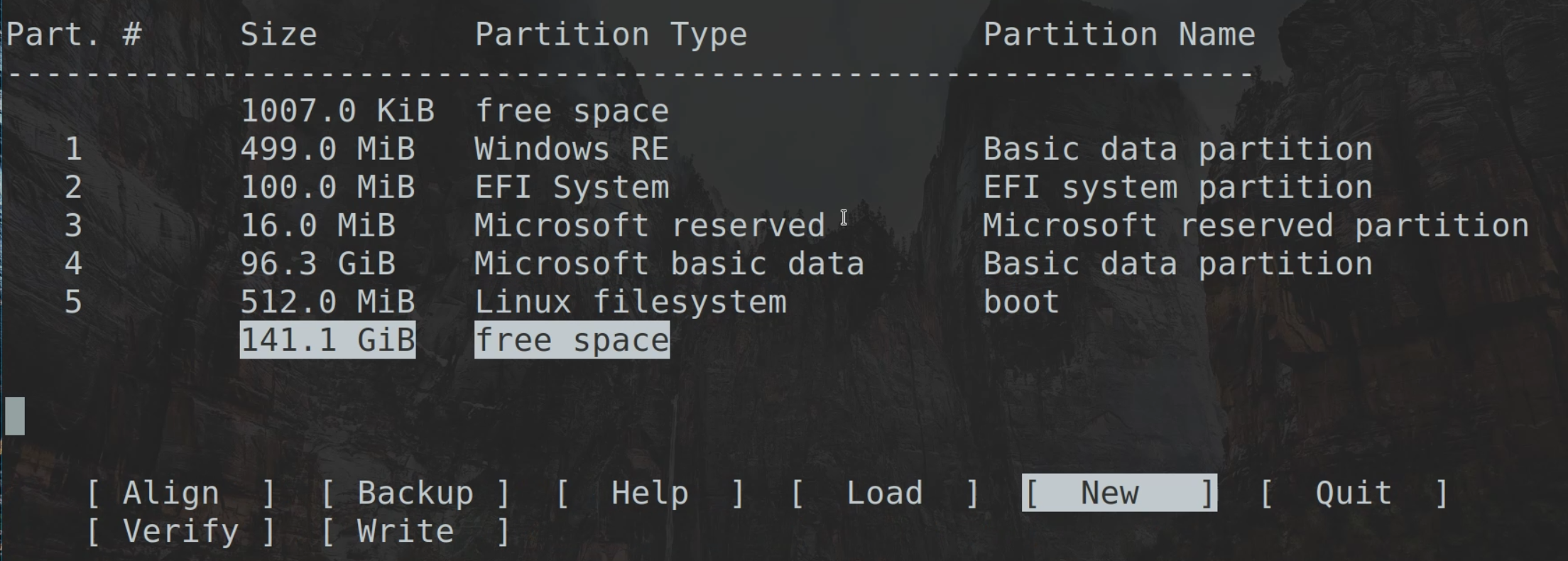
-
Note the partition number of the EFI System partition. This will be referenced later when configuring grub. In the screenshots above, it is partition 2.
-
Select the free space.
-
Choose
[ New ]. -
Enter no value for First sector (chooses default).
-
Enter no value for size in sectors (chooses default).
This will fill the remaining disk.
-
Enter no value for Hex code or GUID (chooses default).
-
Name the partition
root.
-
Choose
[ Write ]and say yes. -
Choose
[ Quit ].
Encrypting and Configuring the Root Partition
-
Encrypt the root partition.
cryptsetup -y --use-random luksFormat /dev/nvme0n1p6At the confirmation prompt, be sure to type
YESin uppercase.-y: interactively requests the passphrase twice.--use-random: uses /dev/random to produce keys.luksFormat: initializes a LUKS partition.
-
Open the LUKS device
cryptsetup luksOpen /dev/nvme0n1p6 cryptrootluksOpen: Opens the LUKS device and creates a mapping in/dev/mapper.
-
Run lsblk to view the new volume relationship.
-
Format the boot partitions as an
ext4file system.mkfs.ext4 /dev/nvme0n1p5 -
Format the cryptroot as a
ext4file system.mkfs.ext4 /dev/mapper/cryptroot
Mounting and Installing
-
Mount cryptroot at
/mnt.mount /dev/mapper/cryptroot /mnt -
Create a
bootdirectory at root.mkdir /mnt/boot -
Mount the boot directory to the boot partition.
mount /dev/nvme0n1p5 /mnt/boot -
Create an
efidirectory in/mnt/boot.mkdir /mnt/boot -
Mount the Window's created EFI partition to
/mnt/boot.mount /dev/nvme0n1p2 /mnt/boot/efiThis is the partition you noted in the Disk Partitioning section.
-
Install packages on the root file system.
pacstrap /mnt linux linux-firmware base base-devel grub efibootmgr vim git intel-ucode networkmanagerlinux: linux kernel ( https://www.archlinux.org/packages/core/x86_64/linux ).linux-firmware: linux kernel ( https://www.archlinux.org/packages/core/any/linux-firmware ).base: common packages for Linux ( https://www.archlinux.org/groups/x86_64/base ).base-devel:common package for development in Linux ( https://www.archlinux.org/groups/x86_64/base-devel ).grub: (GRand Unified Bootloader) is a multi-boot loader.vim: text editor.git: version control system.efibootmgr: userspace application used to modify the Intel Extensible Firmware Interface (EFI) Boot Manager.intel-ucode: processor microcode; assumes Intel x86 processor.networkmanager: handles connecting to wireless and wired networks.
-
Generate file system table (fstab) for mounting partitions.
genfstab -U /mnt >> /mnt/etc/fstab-u: Use UUIDs for source identifiers.
System Configuration
This section enters the new Arch Linux system and configures the system.
-
Enter the system root via
arch-chroot.arch-chroot /mnt -
Set the timezone.
ln -sf /usr/share/zoneinfo/MST /etc/localtimeMSTis my zone, yours may vary. -
Set the Hardware Clock from the System Clock, and update the timestamps in /etc/adjtime.
hwclock --systohc -
Uncomment
en_US.UTF-8 UTF-8in/etc/locale.gen.#en_SG.UTF-8 UTF-8 #en_SG ISO-8859-1 en_US.UTF-8 UTF-8 #en_US ISO-8859-1 #en_ZA.UTF-8 UTF-8Modify for your locale.
-
Generate locale.
locale-gen -
Set the
LANGvariable to the same locale in/etc/locale.conf.echo "LANG=en_US.UTF-8" >> /etc/locale.conf -
Set your
hostname.echo "taco" >> /etc/hostname
Initial Ramdisk Configuration
The initial ramdisk is a root file system that will be booted into memory. It aids in startup. This section covers setup and generation of an mkinitcpio configuration for generating initramfs.
-
Add
encrypttoHOOKSin/etc/mkinitcpio.conf(order matters).HOOKS=(base udev autodetect modconf block encrypt filesystems keyboard fsck)HOOKSare modules added to the initramfs image. Withoutencryptandlvm2, systems won't contain modules necessary to decrypt LUKs. -
Move
keyboardbeforemodconfinHOOKS.HOOKS=(base udev autodetect keyboard modconf block encrypt filesystems fsck) -
Build initramfs with the
linuxpreset.mkinitcpio -p linux
GRUB Bootloader Setup
-
Determine the UUID of your root partition and EFI parition.
blkid
-
Edit the GRUB boot loader configuration.
vim /etc/default/grub -
Update the
GRUB_CMDLINE_LINUXto match the formatcryptdevice=UUID=${ROOT_UUID}:cryptroot root=/dev/mapper/cryptrootwhere${ROOT_UUID}is the UUID captured above.GRUB_CMDLINE_LINUX="cryptdevice=UUID=4f7301bf-a44f-4b90-ad6d-5ec10a0c2f2a:cryptroot root=/dev/mapper/cryptroot" -
Add grub menu item for Windows 10 by editing
/etc/grub.d/40_custom.#!/bin/sh exec tail -n +3 $0 # This file provides an easy way to add custom menu entries. Simply type the # menu entries you want to add after this comment. Be careful not to change # the 'exec tail' line above. if [ "${grub_platform}" == "efi" ]; then menuentry "Windows 10" { insmod part_gpt insmod fat insmod search_fs_uuid insmod chain # use: # after --set=root, add the EFI partition's UUID # this can be found with either: # # a. blkid # - or - # b. grub-probe --target=fs_uuid /boot/efi/EFI/VeraCrypt/DcsBoot.efi # search --fs-uuid --set=root $FS_UUID chainloader /EFI/VeraCrypt/DcsBoot.efi } fi -
Replace
$FS_UUIDwith the EFI partition's UUID, found in step 1 of this section.#!/bin/sh exec tail -n +3 $0 # This file provides an easy way to add custom menu entries. Simply type the # menu entries you want to add after this comment. Be careful not to change # the 'exec tail' line above. if [ "${grub_platform}" == "efi" ]; then menuentry "Windows 10" { insmod part_gpt insmod fat insmod search_fs_uuid insmod chain # use: # after --set=root, add the EFI partition's UUID # this can be found with either: # # a. blkid # - or - # b. grub-probe --target=fs_uuid /boot/efi/EFI/VeraCrypt/DcsBoot.efi # search --fs-uuid --set=root 8E12-69DD chainloader /EFI/VeraCrypt/DcsBoot.efi } fi -
Install grub.
grub-installThis assumes your efi is located in
/boot/efi; additional flags are available if you used an alternative location. -
Generate the grub configuration.
grub-mkconfig -o /boot/grub/grub.cfg
User Administration
-
Set the root password.
passwd -
Add a user.
useradd -m -G wheel josh-Gadds the user to a group.-mcreates a home directory.
-
Set the user's password.
passwd josh -
Enter visudo.
visudovisudoedits the sudoers files at /etc/sudoers. It does this safely by acquiring a lock. -
Uncomment the lines that allow users of group
wheelto sudo.## Uncomment to allow members of group wheel to execute any command %wheel ALL=(ALL) ALL
Enable Networking
-
Enable NetworkManager to ensure it starts after boot.
systemctl enable NetworkManager
Rebooting
-
Exit the
arch-chrootexit -
Unmount the partitions.
umount -R /mnt -
Reboot.
reboot -
Using grub, login to Arch linux.
-
Use
nmtui-connectto establish internet and begin installing packages.From here you can install any window manager such as: